And sensible contracts can mechanically execute AI-driven choices, creating autonomous techniques for insurance claims, supply chain optimisation and personalised financial companies. As the founder and CEO of Krown Applied Sciences Inc., I’ve dedicated my career to constructing the world’s largest blockchain ecosystem secured with post-quantum cryptography. My work throughout Smart contract blockchain safety, cryptographic governance and digital asset protection has supplied firsthand insight into the scale of the quantum security challenge—and the urgency of addressing it. These improvements assist stop attacks, protect user data, and build more reliable techniques.
By incorporating strong audit trails, organizations can feel assured that any modifications are absolutely documented and can be reviewed, embracing each flexibility and accountability. It’s truthful to say that no distributed ledger technology is prone to match this efficiency in the near term, or perhaps ever. You can invest by shopping for cryptocurrencies together with Bitcoin or Ethereum that run on a blockchain. Alternatively, think about buying shares in companies developing blockchain options, or blockchain-focused funds. Blockchain is rapidly altering monetary services through cryptocurrency payments, decentralised finance (DeFi) and streamlined banking operations.
Safety Of Consensus Mechanism
Even skilled users have been tricked into revealing sensitive information when the attacker’s deception is subtle sufficient. Too much openness invites Sybil vulnerabilities; an excessive quantity of restriction dangers undermining decentralization. Proof of Work makes it expensive to operate many nodes by requiring vital computational assets. Proof of Stake ties affect to the amount of cryptocurrency a participant owns and is prepared to lock up. Wealth focus in PoS systems and the rise of mining swimming pools in PoW techniques each create situations the place influence may be quietly consolidated.
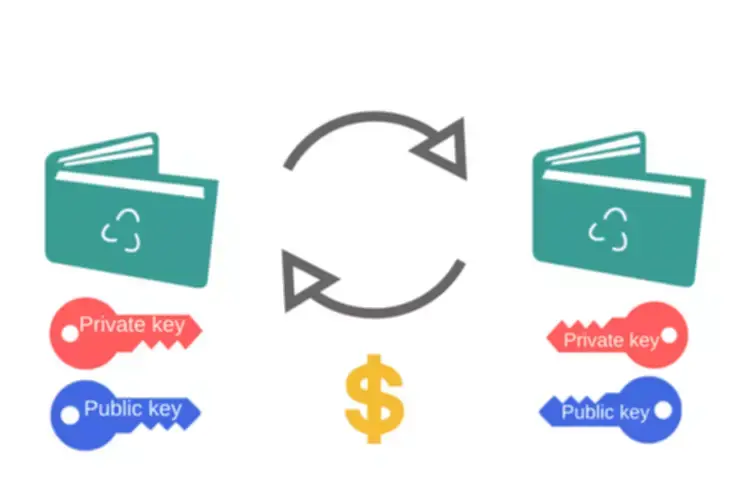
From smart contract exploits and cross-chain bridge hacks, to phishing campaigns that drain users wallets, the risks going through blockchain expertise are evolving in actual time. In this weblog, we’ll discover essentially the most pressing blockchain security challenges and the steps participants can take now to build extra resilient infrastructure. Quantum computer systems may extract private keys from public keys, rendering whole blockchain wallets utterly compromised. Quantum technology-enabled malicious customers can, in theory, steal cash, impersonate legitimate users, and alter transaction histories. Blockchain offers blockchain trends robust built-in safety, but it’s not resistant to threats—especially when utilized in large-scale operational environments. From coding flaws in sensible contracts to user-targeted attacks like phishing and malware, many dangers emerge on the edges of the system.
Forms Of Blockchains
In its annual report, the US Office of the Comptroller of the Forex (OCC) mentioned more sophisticated phishing attacks goal workers who have entry to credentialed information. The report suggests a multi-layered safety protocol to decentralize threat — precisely what blockchain can present. Here are three early adopters among “traditional” Wall Road banks that use blockchain technology to protect their most essential data. Quantum computing, once a futuristic idea, is rapidly becoming https://www.xcritical.com/ a actuality, posing a major problem to the cryptographic security of Bitcoin. The future security of Bitcoin against quantum attacks hinges on safeguarding wallets and transactions, which could probably be easily compromised by superior quantum know-how. These schemes can potentially be used in blockchain key trade protocols, digital signatures, and identification verification methods.
Blockchain Safety Tips And Best Practices
This collaboration exemplifies how business leaders and neighborhood organizations can work collectively to help protect software program provide chains. Blockchain networks face significant throughput limitations in comparison with conventional payment methods. For example, Bitcoin processes roughly 7 transactions per second, while Ethereum handles around 15.
Regardless Of its inherent strengths in cryptography and consensus algorithms, blockchain remains prone to various threats, from smart contract vulnerabilities to phishing assaults. Subsequently, implementing greatest practices is important, corresponding to regular audits, secure key administration, and ongoing person schooling. Blockchain safety is the inspiration of belief and reliability in decentralized systems.
- Proper testing, auditing, and formal verification are essential to counter these blockchain security points.
- Digital signatures add a layer of accountability, as each signature is unique to the personal key holder, making it troublesome for malicious actors to pretend.
- One frequent menace, a sybil attack, includes an attacker including a bunch of bogus participants to a blockchain network.
- This process ensures that each transaction is true and correct, constructing confidence in the blockchain technology’s security measures – no more questions like, “Is blockchain safe?
- Unfortunately, as their recognition has grown, so has attackers’ interest in targeting them.
- Moreover, as a geographically distributed network of nodes, it is potential to provide service the nodes experiencing an attack could go down, but other nodes would fall again to keep offering service.
As organizations more and more use distributed ledger technologies for his or her most sensitive operations, blockchain safety has become a key cornerstone of the digital financial system. Conventional blockchain safety is dependent upon cryptography such as RSA and ECC (elliptic curve cryptography), which ensures data integrity and authenticity in opposition to unauthorised entry. Such cryptography is immune to conventional computer systems but prone to quantum algorithms which have the flexibility to decrypt cryptography by factoring large prime numbers much quicker than current supercomputers. This implies that once quantum computer systems come into regular use, they will decrypt the blockchain encryption, revealing transactions, digital coins, and consumer identities.
The distribution of solely certain data to credentialed healthcare professionals ensures that cybercriminals can’t access all identifiable aspects of an individual’s well being report. This includes rigorous testing, formal verification, and peer evaluate before deployment. The cost of auditing code is small in comparability with the potential losses from an exploit. No matter how decentralized and cryptographically safe a blockchain could additionally be, it ultimately interacts with human beings — and human beings are vulnerable to persuasion, worry, and greed. The illusion of invincibility has made some initiatives complacent, underestimating the ingenuity of attackers who’re as motivated as the blockchain developers themselves. The result has been a growing listing of breaches, many of which have exploited not the cryptography, but the surrounding infrastructure.